An SSH key is a form of authentication in the SSH protocol. It is similar to a password, but allows for authentication without entering in a password or any manual input. SSH keys generally speaking are more secure, and convenient than password authentication.
Generating Keys
Command Line
If you currently have access to SSH on your server, you can generate SSH keys on the command line using the ssh-keygen utility which is installed by default on our servers. Run it on your server with no options, or arguments to generate a 2048-bit RSA key pair (which is plenty secure).
$ ssh-keygen
You will be prompted to select a file for the key pair. The default directory for SSH keys is ~/.ssh with the private key named id_rsa and the public key named id_rsa.pub. By using the default file names, the SSH client will be able to automatically locate the keys during authentication so it is strongly recommended to not change them. You can use the default by pressing the Enter key.
Generating public/private rsa key pair. Enter file in which to save the key (/home/USER/.ssh/id_rsa):
If /home/USER/.ssh/id_rsa or a key of the name you chose already exists, you will be prompted to overwrite the keys. If you do overwrite the existing keys, you will not be able to use them to authenticate anymore.
After you have selected the file for the key pair, you be will be prompted to enter a passphrase to encrypt private key file. Encrypting the private key with a passphrase is optional, but it will improve security the keys. If you enter a passphrase you will have to provide each it time you use the key. You can press the Enter key to not use a passphrase; we strongly recommend the use of a passphrase with SSH keys.
Created directory '/home/USER/.ssh'. Enter passphrase (empty for no passphrase): Enter same passphrase again:
A public and private key will now be generated.
Your identification has been saved in /home/USER/.ssh/id_rsa. Your public key has been saved in /root/.ssh/id_rsa.pub. The key fingerprint is: SHA256:boo2WmwU41qy/IxmJCgDjjsg7xvvcXmHhHa7BKhoCPY root@server.domain.tld The key's randomart image is: +---[RSA 2048]----+ | | |o | |+. . . . | |=o. o . + o | |O+.. = .S= o | |X=oEo o.o = + | |*+= . ooo o | |oO+. ..o . | |*+.+. . | +----[SHA256]-----+
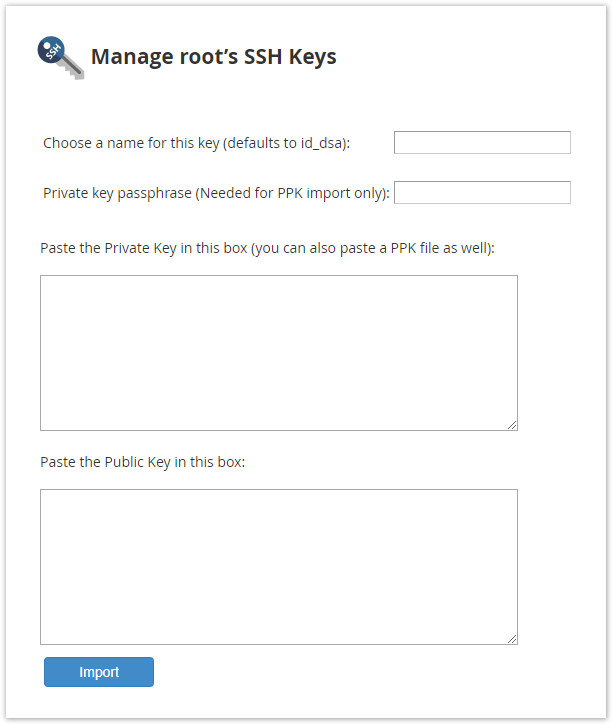
WHM
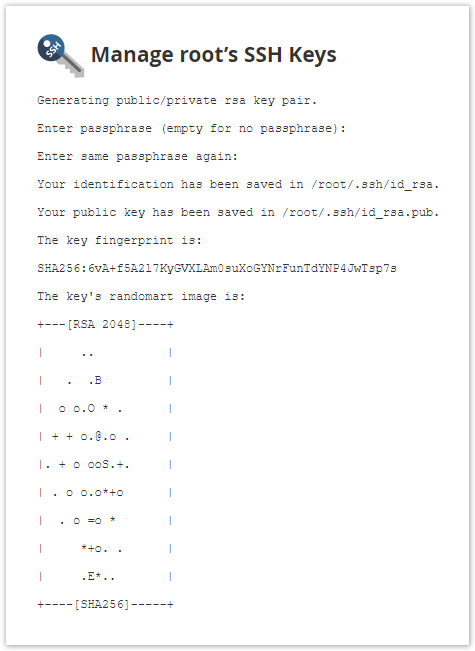
You can generate SSH key pairs for root in WHM >> Home Security Center >> Manage root's SSH Keys.
Click Generate a New Key to get started.
There are several fields on this page: Key Name, Key Password, Key Type, and Key Size.
The default Key Name is id_rsa. Keys are generated in /root/.ssh/ so the default key name would create a private key in /root/.ssh/id_rsa, and a public key in /root/.ssh/id_rsa.pub. Using the default name will allow SSH clients to automatically locate the keys so it is strongly recommend you use the default name (simply leave the field blank or fill it with id_rsa).
The Key Password encrypts the private key file using a password to add an extra layer of security. The password must be provided each time the key is used for authentication to decrypt the private key. The Password Strength field indicates how strong your password is. 0 indicates a very weak password, and 100 indicates a very strong password. Click Password Generator to have a strong password generated for you.
Key Type and Key Size are RSA and 2048 by default, and are secure enough for most purposes so these can be left alone.
Click Generate Key to generate the SSH key pair. WHM will then display the location of the key.
PuTTY
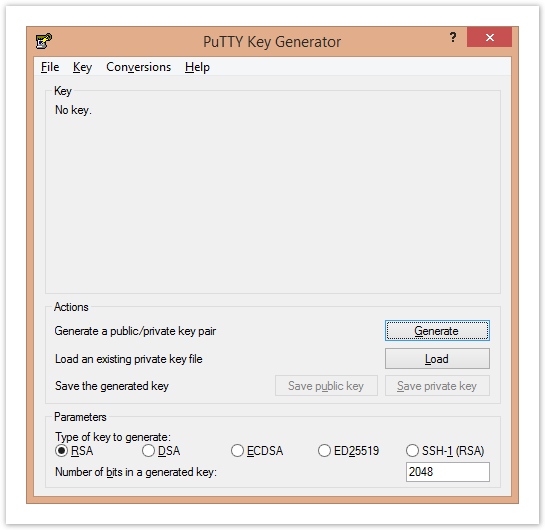
PuTTY is an open Windows SSH client. You will need to have the PuTTYgen utility installed to generate an SSH key pair. PuTTYgen is included in Windows installer on the Download PuTTY site, but you can download it separately if you installed PuTTY without its extra utilities. See Connect using Putty to a Linux Server to learn more about PuTTY.
Open PuTTYgen.
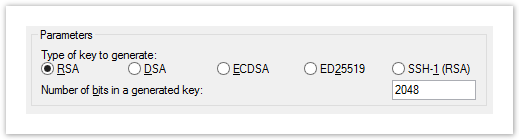
The Parameters at the bottom can be adjusted to affect how secure the key is, but the default options are plenty secure for most purposes.
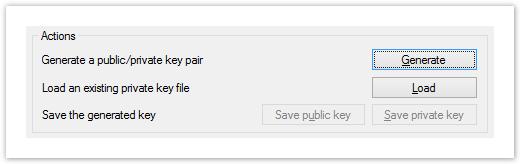
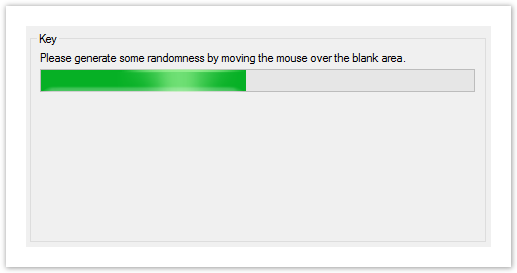
If you're satisfied with the parameters, click Generate in Actions to generate the key pair.
You may be asked to "generate some randomness by moving the mouse over the blank area" to generate the key. The randomness is used to generate your keys securely, and make it difficult to reproduce them.
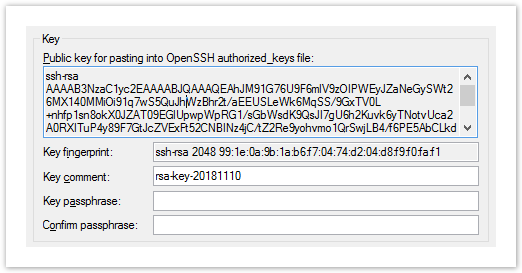
Once the key is generated, you will see the public key in PuTTYgen.
The Key passphrase field sets a password used to decrypt the private the key. This field is optional, and the private key will not be encrypted if it is omitted.Using a passphrase increases the security of your SSH keys, and we strongly recommend setting one.
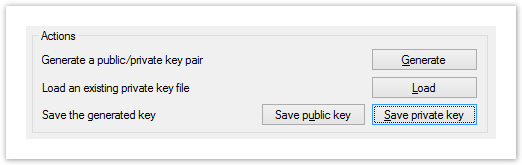
Be sure to save both the public and private keys on your local machine so they can be used by PuTTY for authentication in the future by clicking the Save public key and Save private key buttons.
If you don't use a passphrase, it will prompt you to confirm before allowing you to save the private key. The private key will be saved as a .ppk file. The public key isn't given an extension by default, but .pub is a common extension for public key files. It can be saved as a .txt file as well as the public key file only stores the public key in plain text.
Uploading Keys
Command Line
If you currently have access to SSH on your server, you can upload the key over the command line.
Retrieve the contents of the public key. If the key was created in the default location, this can be done by outputting the contents of ~/.ssh/id_rsa.pub.
$ cat ~/.ssh/id_rsa.pub
The output will look similar to the following:
ssh-rsa AAAAB9NzaC1yc2EAAAADAQABAAABAQDBej/3XAjhwTwWXsOJmDdKTLtjnpGXsHOAEIYC12qQ r51+AVJPNsqcDlFdv+Lr/XufQDCh2gXz+ieA/LJNb5luxReaVVbKtvAONZgv8uLD1J8kzRXike3h9L53 oIo2j8Lt4fuzB8yAWkwBelurn4OWfk0K6gFXN86RgprKSPN3GbwG6MINAor7NwCHzJhVK9u6Jpw9EPJv Dl4co+N9L+CGgudvY7iBNzIofE9MP68lXcql4bMWz3+2H0FWKHZ1rSJz56KjoCKBPWTqdFq5o1AIcauc ECgiTaEGcSNk4+T0A8BuAOd3a4O9Gr6y8C4Sn4ghYajJVWsszP2B1tTGAc3L
Open the (and create if it doesn't exist) ~/.ssh/authorized_keys file using a text editor such as nano, pico, or vim.
$ nano ~/.ssh/authorized_keys
If you had to create the ~/.ssh/ directory, or the authorized_keys file, you need to verify the permissions are correct, or you won't be able to login.
$ chmod 700 ~/.shh
$ chmod 600 ~/.ssh/authorized_keys
Paste the public key at the bottom of the file, and then save and close the file.
Alternatively, you can append the public key to ~/.ssh/authorized_keys with a single command.
You can use the cat command if the public key is stored in a file.
$ cat ~/.ssh/id_rsa.pub >> ~/.ssh/authorized_keys
If the public key is not stored as a file on the server, you can use the echo command.
$ echo "ssh-rsa AAAAB9N...sszP2B1tTGAc3L" >> ~/.ssh/authorized_keys
Be sure to include the entire public key in quotes after echo.
Once the public key is added to the authorized_keys file, you should be able to login using your SSH keys.
WHM
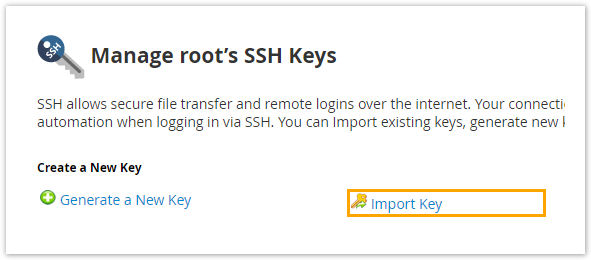
You can import an existing SSH key for root in WHM >> Home Security Center >> Manage root's SSH Keys.
Click Import Key.
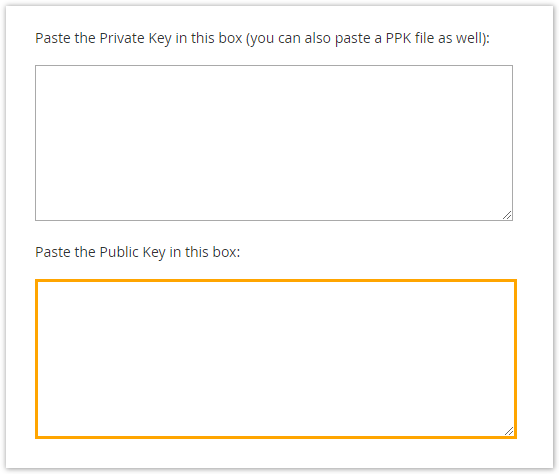
The next page has a few fields to fill in.
You need to name the SSH key in the Choose a name for this key field. The default key name is id_rsa. Using the default name will allow SSH clients to automatically locate the keys so it is strongly recommend you use the default name (simply leave the field blank or fill it with id_rsa).
If you are importing a PPK (PuTTYgen key) file, enter its password (if applicable) in the Private key passphrase text box.
Paste the public key into the appropriate box, but do not paste the private key into the box; private keys should always remain on the servers that generated them.
Click Import.
WHM will display the name of the keys imported, and you should now be able to authenticate over SSH using the key.
Custom Key Names
The default name for SSH key pairs is id_rsa, and that name will allow an SSH client to locate the key automatically. When an SSH key pair doesn't use the default name, you will need to specify the name of key used.
$ ssh user@server.domain.tld -i /path/to/ssh/key